A researcher has created a website that uses your installed Google Chrome extensions to generate a fingerprint of your device that can be used to track you online.
To track users on the web, it is possible to create fingerprints, or tracking hashes, based on various characteristics of a device connecting to a website. These characteristics include GPU performance, installed Windows applications, a device’s screen resolution, hardware configuration, and even the installed fonts.
It is then possible to track a device across sites using the same fingerprinting method.
Fingerprint from installed Chrome extensions
Yesterday, web developer ‘z0ccc’ shared a new fingerprinting site called ‘Extension Fingerprints’ that can generate a tracking hash based on a browser’s installed Google Chrome extensions.
When creating a Chrome browser extension, it is possible to declare certain assets as ‘web accessible resources’ that web pages or other extensions can access.
These resources are typically image files, which are declared using the ‘web_accessible_resources‘ property in a browser extension’s manifest file.
An example declaration of web-accessible resources is shown below:
"web_accessible_resources": [
{
"resources": [ "logo.png" ],
"matches": [ "https://www.bleepingcomputer.com/*" ]
}
],As previously disclosed in 2019, it is possible to use web-accessible resources to check for installed extensions and generate a fingerprint of a visitor’s browser based on the combination of found extensions.
To prevent detection, z0ccc says that some extensions use a secret token that is required to access a web resource. However, the researcher discovered a ‘Resource timing comparison’ method that can still be be used to detect if the extension is installed.
“Resources of protected extensions will take longer to fetch than resources of extensions that are not installed. By comparing the timing differences you can accurately determine if the protected extensions are installed,” explained z0ccc on the project’s GitHub page.
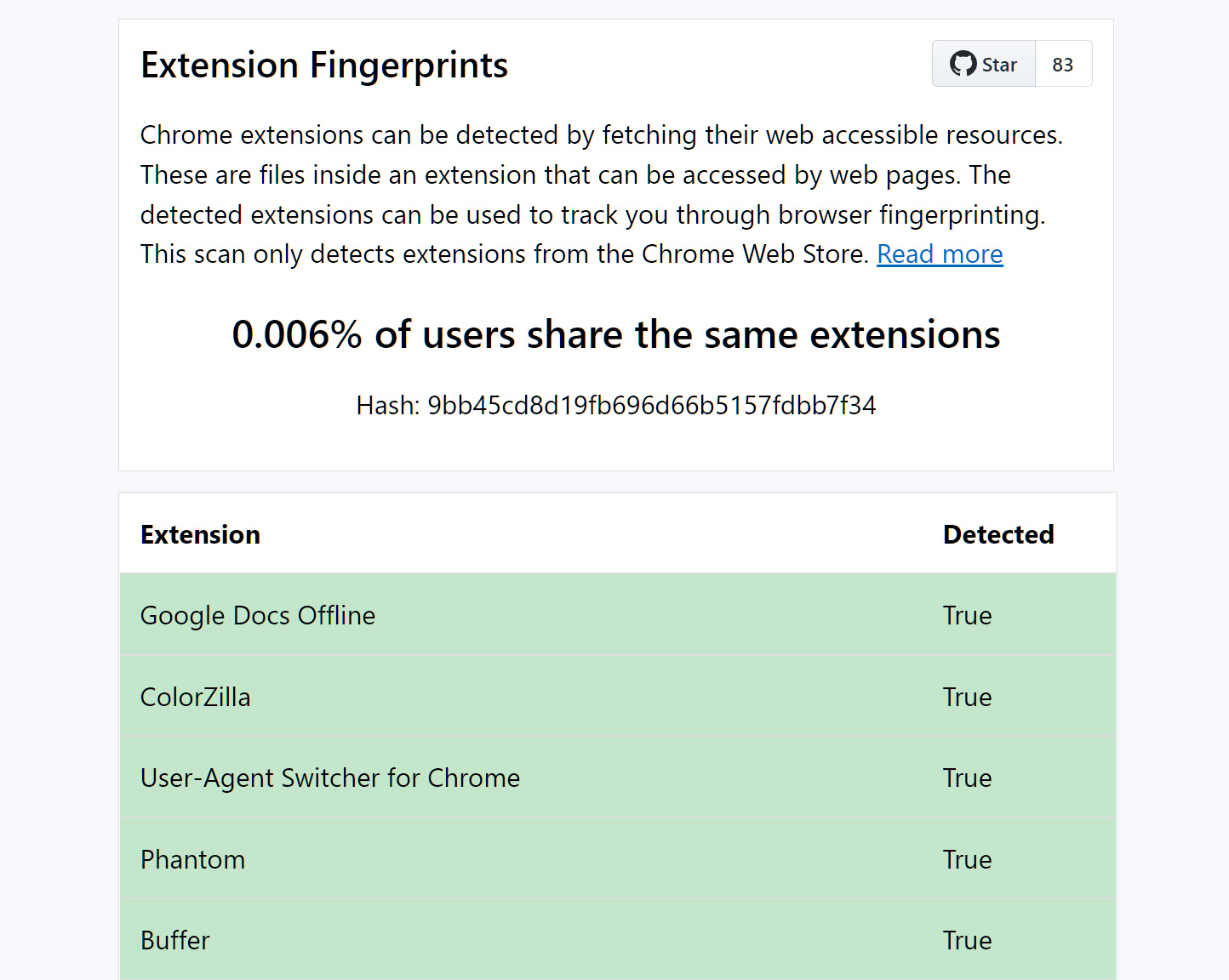
To illustrate this fingerprinting method, z0ccc created an Extension Fingerprints website that will check a visitor’s browser for the existence of web-accessible resources in 1,170 popular extensions available on the Google Chrome Web Store.
Some of the extensions that the website will identify are uBlock, LastPass, Adobe Acrobat, Honey, Grammarly, Rakuten, and ColorZilla.
Based on the combination of installed extensions, the website will generate a tracking hash that can be used to track that particular browser, as shown below.
Source: BleepingComputer
Some popular extensions, such as MetaMask, do not expose any resources, but z0ccc could still identify if they are installed by checking if “typeof window.ethereum equals undefined.”
While those with no extensions installed will have the same fingerprint and be less useful for tracking, those with many extensions will have a less common fingerprint that can be used to track them around the web.
However, adding other characteristics to the fingerprinting model can further refine the fingerprint, making the hashes unique per user.
“This is definitely a viable option for fingerprinting users,” z0ccc explained in an email to BleepingComputer.
“Especially using the ‘fetching web accessible resources’ method. If this is combined with other user data (like user agents, timezones etc) users could be very easily identified.”
with no extensions
The Extensions Fingerprints site only works with Chromium browsers installing extensions from the Chrome Web Store. While this method will work with Microsoft Edge, it would need to be modified to use extension IDs from Microsoft’s extension store.
This method does not work with Mozilla Firefox add-ons as Firefox extension IDs are unique for every browser instance.
uBlock is the most commonly installed
While z0ccc is not collecting any data regarding installed extensions, his own tests showed that uBlock installed is the most common extension fingerprint.
“By far the most popular is having no extensions installed. As previously said I do not collect specific extension data but in my own testing it seems that having only ublock installed is a common extension fingerprint,” shared z0ccc.
“Having 3+ detectable extensions installed seems to always make your fingerprint very unique.”
Below are the percentages of users with various popular extensions installed from tests conducted by BleepingComputer.
- 58.248% – No extensions installed or enabled.
- 2.065% – Only Google Docs Offline, which is the only extension installed by default.
- 0.528% – uBlock Origin + Google Docs Offline
- 0.238% – AdBlock + Google Docs Offline
- 0.141% – Adobe Acrobat + Google Docs Offline
- 0.122% – Google Translate + Google Docs Offline
- 0.019% – Malwarebytes Browser Guard
- 0.058% – Grammarly + Google Docs Offline
- 0.058% – LastPass + Google Docs Offline
- 0.051% – Honey + Google Docs Offline
- 0.013% – ColorZilla + Google Docs Offline
In our tests, installing three to four extensions brought the percentage of users using the same extension to as low as 0.006%. Obviously, the more installed extensions, the fewer people will have the same combination installed.
z0ccc says the 0.006% percentage indicates that you are the only user with that combination of extensions, but this will change as more people visit the site.
Extension Fingerprints has been released as an open-source React project on GitHub, allowing anyone to see how to query for the presence of installed extensions.
Update 6/19/22: Clarified that z0ccc did not discover the method to detect installed extensions but rather the timing comparison method.

